BitFlip: A Randomness-Rich Cipher
Internationally Validated
 . .
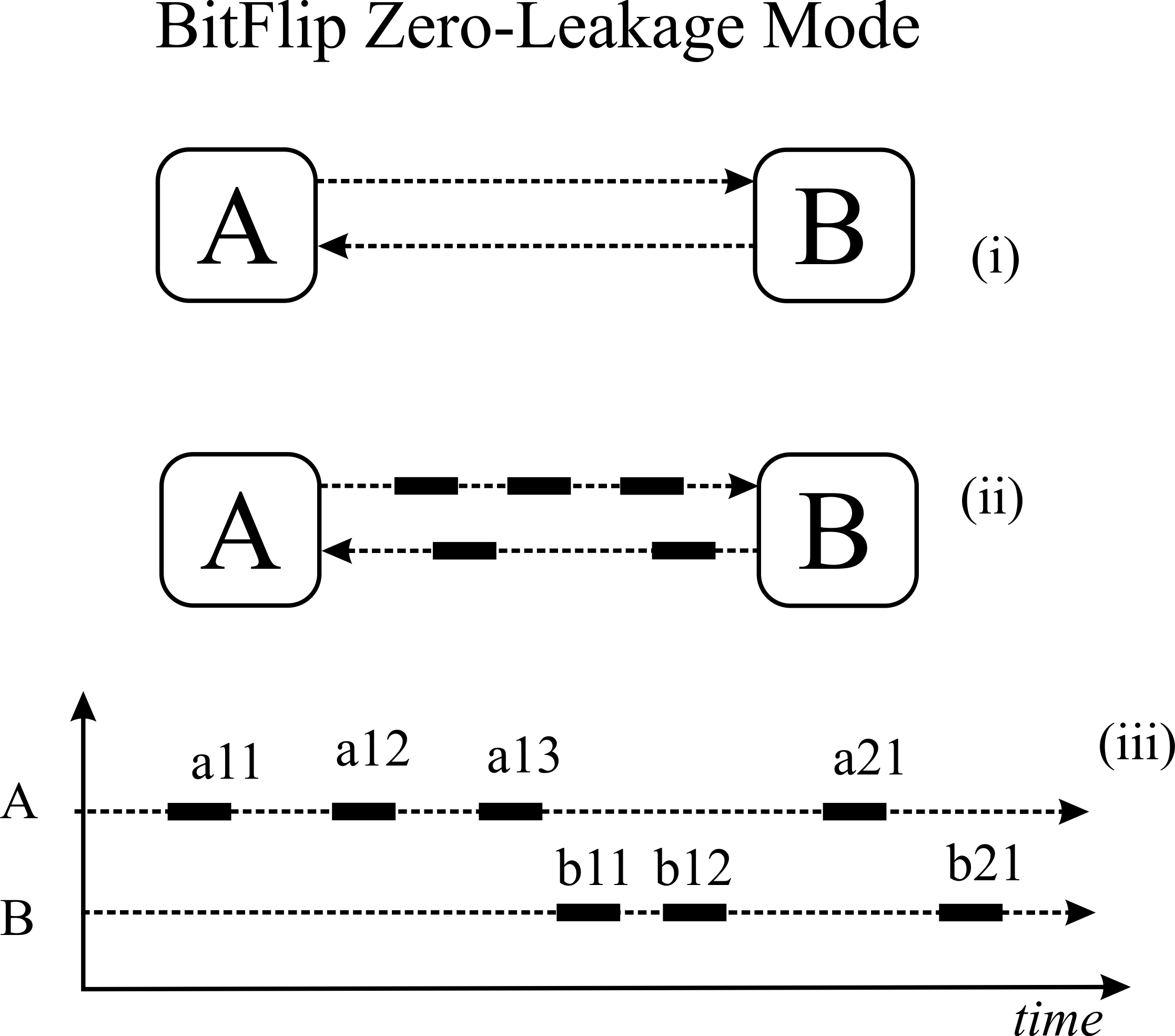
In Quantum Cryptography one communicates bits which the intruder cannot determine their identity. As the bits fly by, each bit can be zero or one in equal likelihood. The technology for this quantum equivocation is still in the lab, but its security benefit can be efficiently emulated with available engineering. We transmit a message with 50% of the bits being flipped. Any intruder holding each bit will face a quantum-like equivocation: is this bit what it says it is, or is it the opposite? To properly implement this scheme we need to deploy quantum-grade randomness to select which bits to flip. The technology to do so is now commercially available. We design our BitFlip ciphers on the specifications of a remarkable Swiss company: IDQ, manufacturing quantum-grade randomness generators that fit on BitFlip boards.
 . .
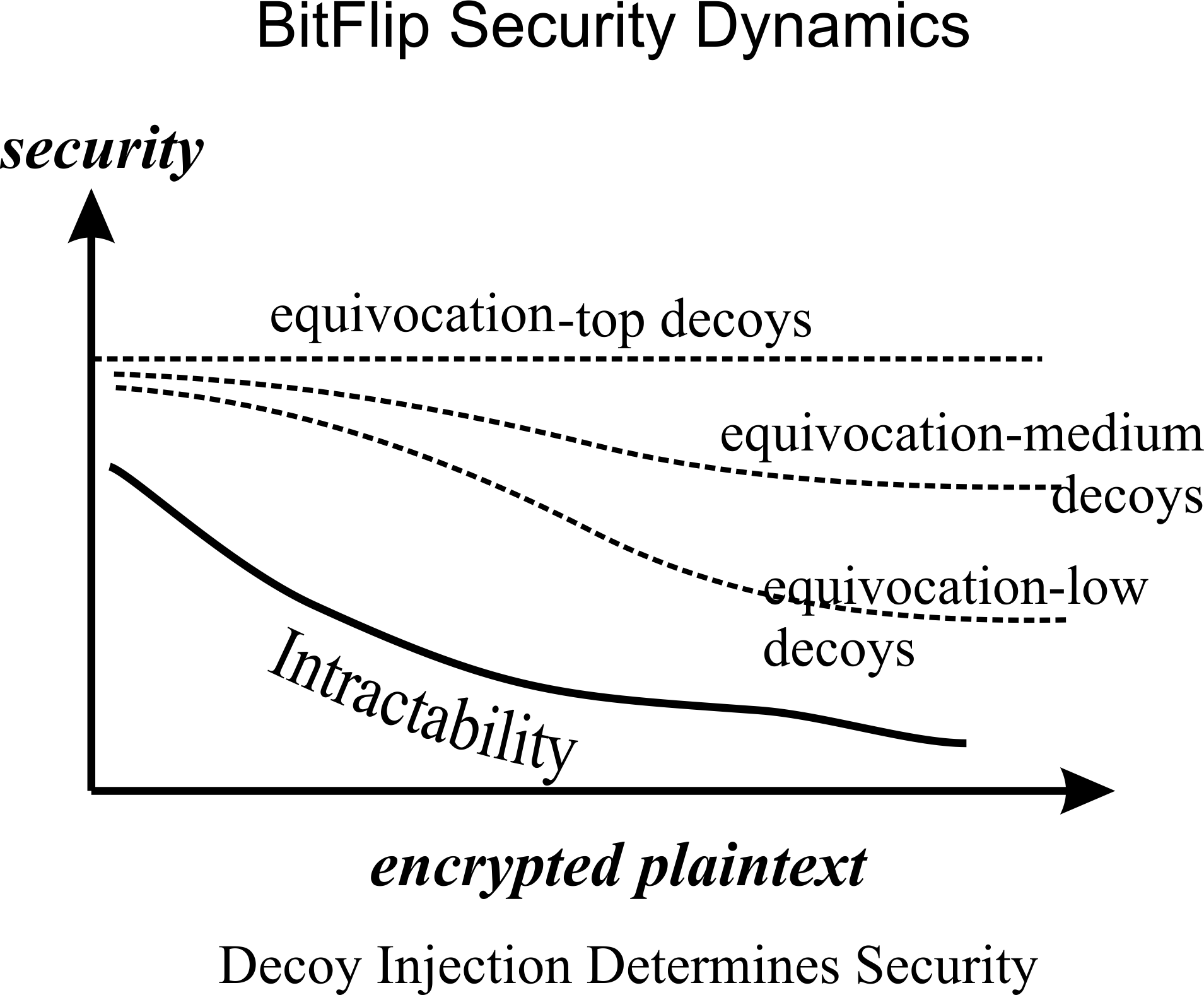
Both the equivocated transmission and its decryption are processed with ultra fast dedicated chips that are simply counting bits and flipping them. The BitFlip user determines how much security to use for his or her data, by determining how much randomness to use. As the scholarly references below prove, with enough randomness BitFlip will achieve quantum-grade security.
BtFlip is battery friendly and therefore fit for IoT applications, it allows for parallel encryption of several messages in a mix, and hence it is ideal for project control, complexity management, and blockchain applications. BitFlip protocols may be applied with a steganographic edge -- hiding the nature and the extent of the communication, not only its content.
BitFlip was tested by the most prestigious IT testing institution in Germany, and here is their summary:
BITFLIP ANALYSIS EVALUATION REPORT
TUV Informationstechnik GmbH - Evaluation Body for IT Security
Executive Summary and Open Questions
BitFlip is a viable new type of cryptography based on generous use of high quality random- ness combined with simple, fast, computation, as opposed to the algorithmic complexity used by the current mainstay ciphers. In course of the BitFlip Analysis project TUV Infor- mationstechnik GmbH analyzed the basic properties of the cipher’s core primitive.
It turned out that in order to keep the ciphertext indistinguishable from a random series the key sizes need to be very large, e.g. 1000 bits or longer. We detected indications that shorter keys (e.g. 12 bit) might allow for strong- and standard-ciphertext-only attacks. However, an actual exploit is subject of further research.
On the other hand, by design, BitFlip allows throwing in complementary security features like addition of decoy messages and balancing letter frequency. While the analysis of these features is beyond the scope of tests documented in this report, a recent publication (2) offers a mathematical proof that a BitFlip user can mix the message with increasing quantities of random bits to increase the security at will. And by that, the security is scalable! So, it appears that BitFlip's strength does not only come from the core primitive itself, but from the ease of adding additional security on the fly.
Also, the existence of collisions, as observed in our tests, may actually be turned into an advantage for the cipher's security as indicated by a Giesecke & Devrient proposal(3).
In summary, the suitability of BitFlip and its augmentations as a new kind of crypto technology for high-end financial security, and the burgeoning Internet-of-Things market is a highly credible proposition, but more investigation is needed to (a) optimize its operating parameters, and (b) examine its premise to be battery-friendly, and as such very fitting for IoT cryptography.
2. https://eprint.iacr.org/2018/084.pdf
3. Digital Money Library, BitFlip Encryption Algorithm, Reflections on a new technology, Giesecke & Devrient, Version 0.9, Printed on 2nd December 2017
TUV Informationstechnik GmbH – Evaluation Body for IT Security, Langemarckstr. 20, 45141 Essen, Germany * Feb 12, 2018
Scholarly Articles
BitFlip: A Randomness Rich Cipher.
Threat Adjusting Security.
 . .
 . .
 . .
|